Anyone who optimizes for growing their viewership or audience, from independent authors to businesses, is foolish to ignore search engine optimization (SEO). Like it or not, it works, driving content to more potential viewers.
And where there’s a system to game, there’s a marketplace of solutions to help you game it.
He alludes to the fact that generative AI (GenAI) platforms are going to incorporate ads, and I’m sure they’ll dominate the advertising ecosystem over time. The unexpected thought that his article provoked: what will happen to the creator ecosystem, and the millions (billions?) of dollars that have been poured into the SEO industrial complex?
Consider these assertions:
- We’ll find and consume content increasingly via GenAI products like ChatGPT and Perplexity, rather than traditional search engines.
- GenAI will sometimes link back to original sources, either by design (as Perplexity does), by user request, or perhaps original sources will appear as ads?
If these are true, and I believe they are, then there may be a new system to game: being the first to provide authoritative content to GenAI engines in hopes they drive traffic to your source.
The Internet is already being littered with talk of Generative Engine Optimization (GEO). But GEO thus far is focused on how to optimize content structure for summarization and reference by GenAI engines. Step #1 in GEO how-tos is “Do all of the SEO things.” This is surely important in 2024, but where’s the puck going?

If there are predictions to be made:
- We’ll see capitulation in the game of GenAI keep-away.1
- GenAI engines will be increasingly connected and increasingly quick to provide results that blend the best of the models with the best results from the web.
- The new game will be creating content and then feeding it immediately and in specific ways to GenAI engines (effectively “GenAI content stuffing”), resulting in a new way of thinking about “authority” or “rank” that increasingly cuts out traditional search engines.
Search engines aren’t going away overnight, or even in the next decade. But they’re a costly means to an end for both creators, who have to optimize for them, and GenAI platforms, which have to wait on them, potentially license results from them, and generally depend on them. For both of these constituencies, the search engine becomes both a boat anchor and a tax, and both will be increasingly motivated to cut them out of the equation.
-
This is a big deal because there’s a considerable effort today to block GenAI crawlers from accessing content. Large publishers might succeed in this, but smaller sites and creators probably won’t. Like water, GenAI crawlers will find a way. ↩
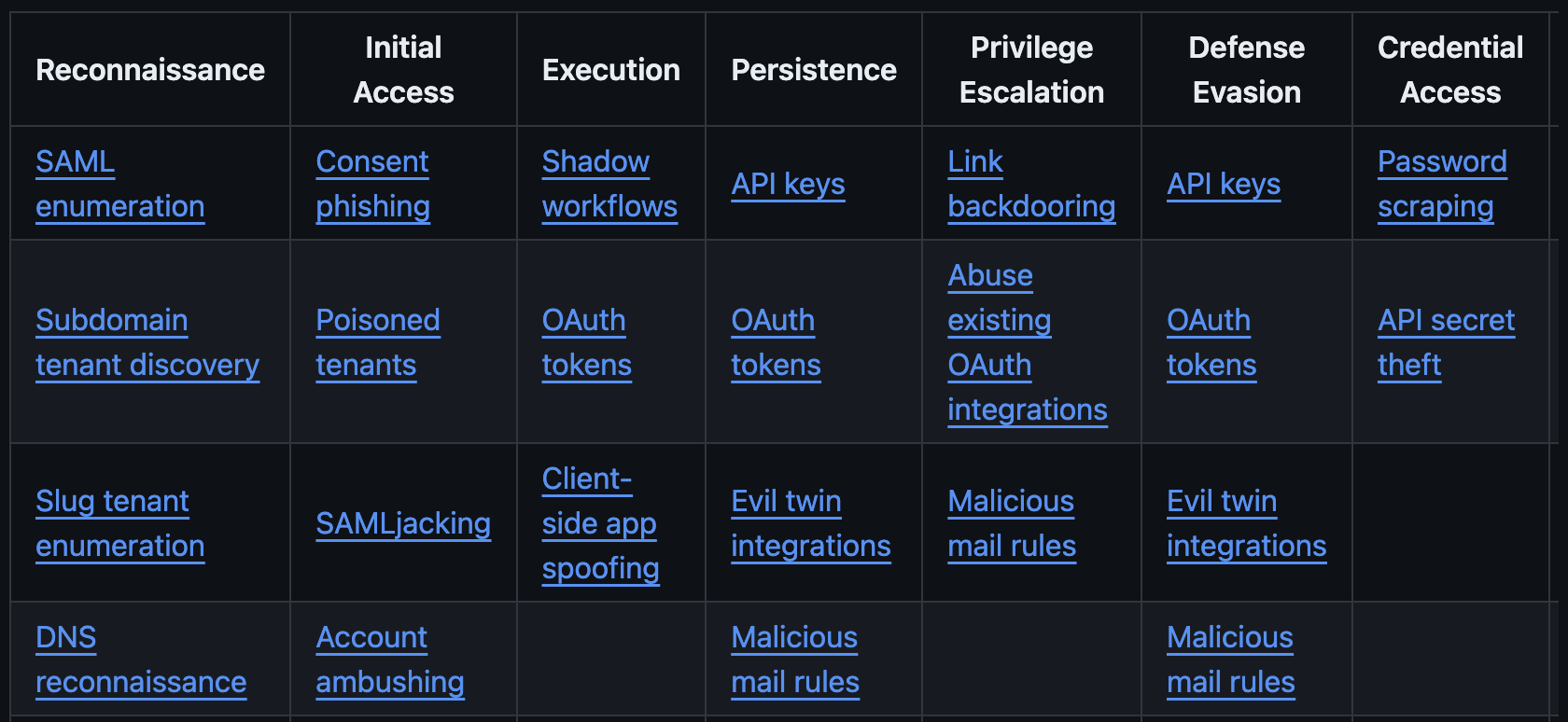
 Above graphic is illustrative, not comprehensive.
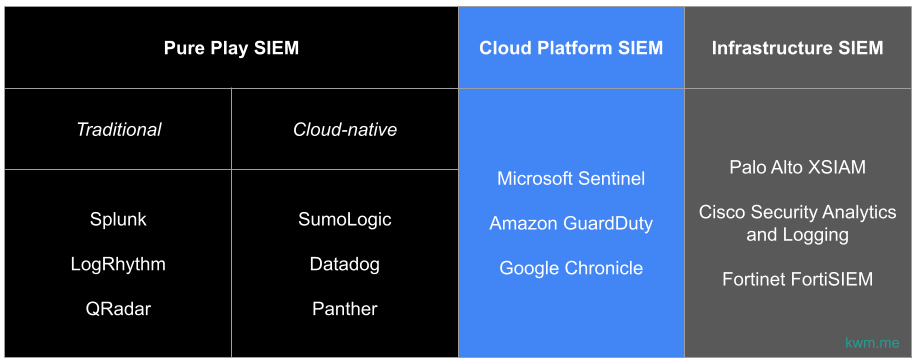
Above graphic is illustrative, not comprehensive.