Simple, measurable ATT&CK testing with Atomic Red Team
Updated January 2025 to support ATT&CK v16.1.
This Google Sheets template aims to make it easy to perform simple, measurable testing of MITRE ATT&CK techniques using Atomic Red Team or an adversary emulation solution of your choosing.
To get started:
- Choose the technique that you wish to test. To help prioritize your testing, incorporate rankings from public threat reports, your own intelligence, or any other mechanism that you choose. The top techniques from Red Canary’s annual Threat Detection Report are incorporated into this template for convenience.
- Select a corresponding Atomic Red Team test. You can search for or browse tests by tactic, technique, or target platform here.
-
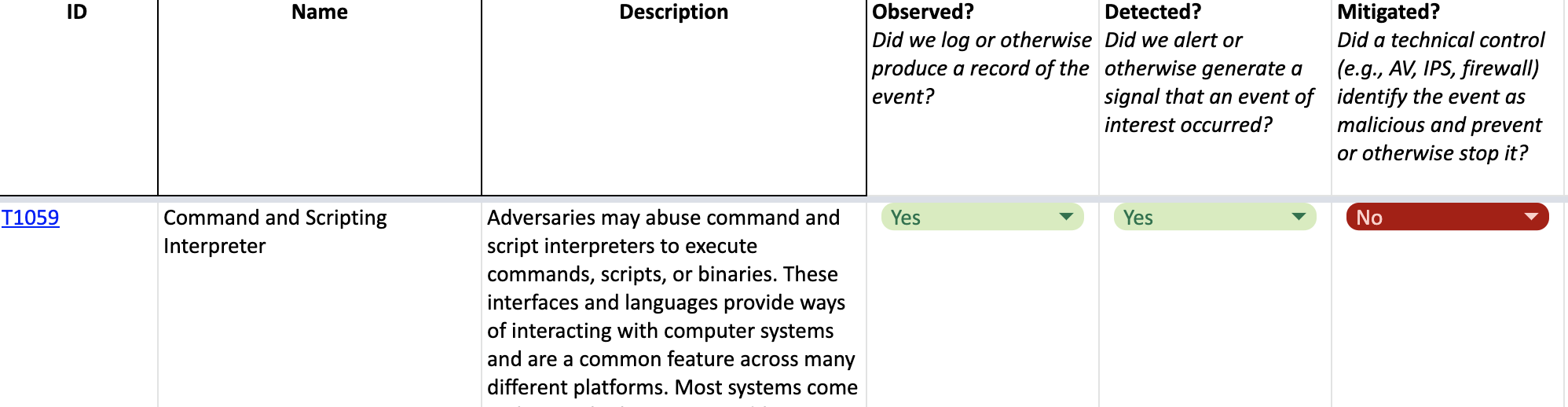
Document whether the test was:
- Observed in any manner, from system logs to network events
- Detected by any of your controls, which could be SIEM analytics, alerts from any of your security products, or activity detected by partners or service providers
- Mitigated by an existing secuirty control
This is based on the “ATT&CK in Excel” spreadsheet provided by MITRE, one of several resources for working with ATT&CK.
