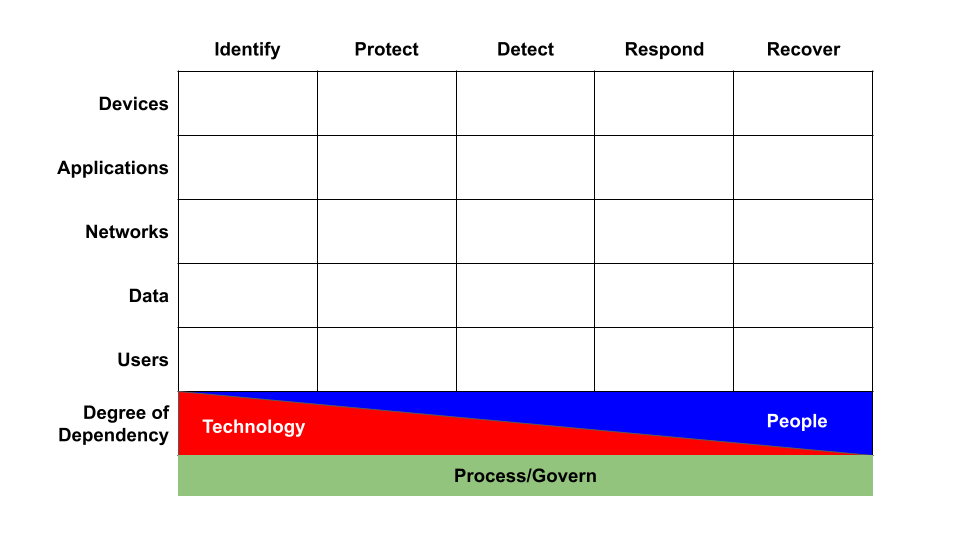
On traditional platforms—such as Windows, macOS, or Linux—knowing who is performing a given activity is useful. However, we can identify an overwhelming percentage of suspicious or malicious activity in the absence of this context.
For example, some software, behaviors, command lines, and changes should be investigated irrespective of identity. We can find a lot of bad things with no identity context at all.
On modern platforms—such as SaaS, IaaS, and PaaS—identity plays a critical role in threat detection and response, thus we describe it as identity threat detection and response, or ITDR. Nothing happens outside of the context of an identity. We can find some bad things without identity context, but virtually all behaviors or changes must be contextualized, baselined, and ultimately investigated in the context of an identity.
To make a weak analogy: On traditional platforms, the process is the data source upon which most detections can be built. On modern platforms, the construct of a process does not exist. On modern platforms, a given identity’s session is the process.
And if you believe that identity is indeed foundational to threat detection on all modern platforms, there are a handful of things that are probably also true:
- Trust is pinned increasingly to identity first, then to devices.
- The browser will become the most important device of all.
- Compromise of an Identity Provider (IdP) and/or browser is an end run around most/all controls.
- Detecting IdP and/or browser compromise is a job that 99% of orgs can’t do, yet.