8-K filings for material cybersecurity incidents should require disclosure of all cybersecurity controls (software and services) in place when the event occurred.
January 17, 2025
8-K filings for material cybersecurity incidents should require disclosure of all cybersecurity controls (software and services) in place when the event occurred.
January 17, 2025
Just a quick note to point out that the Atomic Red Team test tracking tool has been updated to reflect MITRE ATT&CK v16.1.
January 17, 2025
It’s easy to criticize vendors for the number of known exploited vulnerabilities in their software, but raw counts lack context. A company with 100 software products will naturally have more vulnerabilities than one with a smaller portfolio. However, product count alone doesn’t account for a company’s size or resources.
Microsoft is a prime example: as of this writing, it accounts for 311 entries in CISA’s Known Exploited Vulnerabilities (KEV) catalog—25% of all entries. This is often dismissed because of Microsoft’s size and expansive product portfolio. However, a common counterpoint is that its scale affords the company more resources for product security than most.
How do we perform a simple comparison of product security effectiveness across organizations of various sizes, making different types of products for different types of customers? We use the great equalizer: United States Dollars.
Here’s how the CISA KEV leaderboard—specifically the 101 publicly traded companies with the most KEV entries—appears when normalized by market cap:
| Vendor | KEVs | Market Cap (USD) | KEVs per $1B Market Cap |
|---|---|---|---|
| Adobe | 73 | $181,670,000,000 | 0.402 |
| Cisco | 74 | $236,300,000,000 | 0.313 |
| Fortinet | 15 | $70,890,000,000 | 0.212 |
| Atlassian | 13 | $64,200,000,000 | 0.202 |
| Microsoft | 311 | $3,090,000,000,000 | 0.101 |
| Palo Alto Networks | 11 | $114,300,000,000 | 0.096 |
| Oracle | 38 | $437,190,000,000 | 0.087 |
| Samsung | 11 | $245,566,881,889 | 0.045 |
| SAP | 11 | $323,720,000,000 | 0.034 |
| 73 | $2,330,000,000,000 | 0.031 | |
| Apple | 77 | $3,510,000,000,000 | 0.022 |
| D-Link | 20 | $404,068,003 | 0.000 |
Updated 2025-01-15 // Notes: Google = Google + Android; D-Link is a conversion from TWD; Samsung is a conversion from KRW
Nothing’s perfect, but this approach offers a fair way to compare product security effectiveness without relying on subjective or manipulatable criteria. A known exploited vulnerability represents an objectively poor security outcome. Using market cap as the denominator avoids debates over distinctions like product lines, software versions, platforms, and more.
Depending on when this was last updated, there may be more than 10 companies listed due to a tie. ↩
Cybersecurity stat of the day: The average delta (in years) between CVE assignment and addition to the CISA Known Exploited Vulnerability (KEV) catalog is 2.8 years. 🤯
January 14, 2025
I’m a huge fan of Objective-See, Patrick Wardle’s non-profit organization, and the arsenal of invaluable macOS secuirty tools he provides.
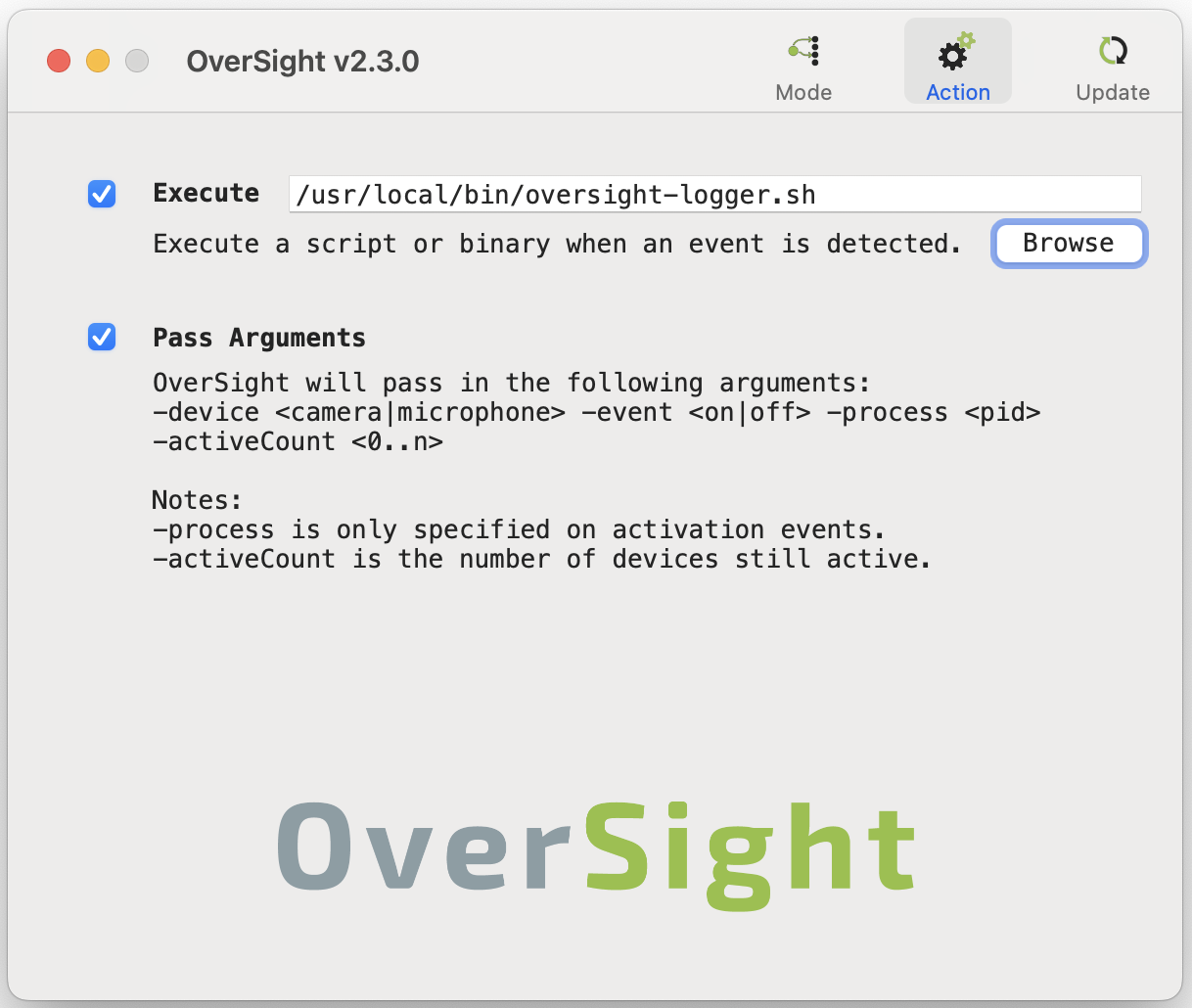
I use Patrick’s OverSight product to monitor camera and microphone activity. By default, OverSight uses notifications to alert you to camera or microphone activity (e.g., when an application activates these devices). In addition to these notifications, I also want to write these events to a log.
OverSight doesn’t have a built-in logging feature, but it does allow you to execute a script when an event is triggered. The Pass Arguments option conveniently passes useful inputs to your script.
oversight-logger is a simple shell script that uses the provided inputs to write sensible log entries when camera or microphone events take place. The only substantive functionality is a pair of functions that look up the process path and process username based on the PID. The resulting log entries will look like this:
2024-12-08 13:45:03 /Applications/zoom.us.app/Contents/MacOS/zoom.us username -device microphone -event on -process 99681 -activeCount 1
2024-12-08 13:45:08 /Applications/zoom.us.app/Contents/MacOS/zoom.us username -device camera -event on -process 99681 -activeCount 2
2024-12-08 13:45:12 NULL NULL -device microphone -event off -activeCount 1
2024-12-08 13:45:12 NULL NULL -device camera -event off -activeCount 0